Disclosure: I have posted the same question already on StackExchange, but since I am not getting any answers there and using Manjaro, I post it here as well. Hope that it’s okay-ish.
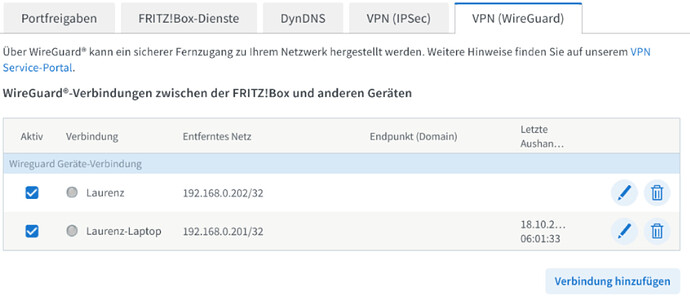
I have set up WireGuard VPN on my router (FritzBox) and added the VPN config to my Manjaro Gnome notebook.
My router in the LAN at home is available on 192.168.0.1.
[Interface]
PrivateKey = xxxx
Address = 192.168.0.201/24
DNS = 192.168.0.1
DNS = fritz.box
[Peer]
PublicKey = xxx
PresharedKey = xxx
AllowedIPs = 192.168.0.0/24,0.0.0.0/0
Endpoint = xxx.myfritz.net:58130
PersistentKeepalive = 25
From the WireGuard logs that I found in the kernel, it seems like the handshake was successful.
sudo dmesg -wT | grep wireguard
[Mo, 16. Okt 2023, 00:43:25] wireguard: WireGuard 1.0.0 loaded. See www.wireguard.com for information.
[Mo, 16. Okt 2023, 00:43:25] wireguard: Copyright (C) 2015-2019 Jason A. Donenfeld <Jason@zx2c4.com>. All Rights Reserved.
[Mo, 16. Okt 2023, 00:55:29] wireguard: wg_config: Interface created
[Mo, 16. Okt 2023, 00:55:29] wireguard: wg_config: Peer 5 created
[Mo, 16. Okt 2023, 00:55:29] wireguard: wg_config: Sending keepalive packet to peer 5 ((einval))
[Mo, 16. Okt 2023, 00:55:29] wireguard: wg_config: Sending handshake initiation to peer 5 ((einval))
[Mo, 16. Okt 2023, 00:55:34] wireguard: wg_config: Peer 5 ((einval)) destroyed
[Mo, 16. Okt 2023, 00:55:34] wireguard: wg_config: Peer 6 created
[Mo, 16. Okt 2023, 00:55:34] wireguard: wg_config: Sending keepalive packet to peer 6 (remote-ip:58130)
[Mo, 16. Okt 2023, 00:55:34] wireguard: wg_config: Sending handshake initiation to peer 6 (remote-ip:58130)
[Mo, 16. Okt 2023, 00:55:35] wireguard: wg_config: Receiving handshake response from peer 6 (remote-ip:58130)
[Mo, 16. Okt 2023, 00:55:35] wireguard: wg_config: Keypair 2 created for peer 6
[Mo, 16. Okt 2023, 00:55:35] wireguard: wg_config: Receiving keepalive packet from peer 6 (remote-ip:58130)
[Mo, 16. Okt 2023, 00:55:45] wireguard: wg_config: Receiving keepalive packet from peer 6 (remote-ip:58130)
[Mo, 16. Okt 2023, 00:55:56] wireguard: wg_config: Receiving keepalive packet from peer 6 (remote-ip:58130)
But still I cannot access the page of my router or any other service in my LAN at home or even do a ping.
The request just time-out.
I’ve read that I need to check if there is a route to my router at 192.168.0.1 over the WireGuard interface, but to me, it seems like there is one:
ip route get 192.168.0.1 ✔
192.168.0.1 dev wg_config src 192.168.0.201 uid 1000
cache
Any idea what is going on there? Are there any additional logs / info that I can provide?
I know that this config works on a different PC.
Edit: Here is the output of sudo wg show while the VPN is active, but i think it doesn’t show anything surprising.
sudo wg show ✔
interface: wg_config
public key: xxxx
private key: (hidden)
listening port: 51820
fwmark: 0xcaed
peer: xxxx
preshared key: (hidden)
endpoint: public-ip:58130
allowed ips: 192.168.0.0/24, 0.0.0.0/0
latest handshake: 2 seconds ago
transfer: 124 B received, 19.25 KiB sent
persistent keepalive: every 25 seconds
Edit #2: Additional information
ip -br link; ip -br addr; ip route; ip rule ✔
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
wlp0s20f3 UP 34:7d:f6:8e:6e:a3 <BROADCAST,MULTICAST,UP,LOWER_UP>
virbr0 DOWN 52:54:00:1b:79:e3 <NO-CARRIER,BROADCAST,MULTICAST,UP>
br-b70272889e99 DOWN 02:42:cf:67:52:3b <NO-CARRIER,BROADCAST,MULTICAST,UP>
docker0 DOWN 02:42:cf:d9:9e:e6 <NO-CARRIER,BROADCAST,MULTICAST,UP>
wg_config UNKNOWN <POINTOPOINT,NOARP,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
wlp0s20f3 UP 192.168.0.62/24 fe80::a493:410e:53d0:9d48/64
virbr0 DOWN 192.168.122.1/24
br-b70272889e99 DOWN 172.26.1.1/24
docker0 DOWN 172.26.0.1/24
wg_config UNKNOWN 192.168.0.201/24
default via 192.168.0.1 dev wlp0s20f3 proto dhcp src 192.168.0.62 metric 600
default via 192.168.0.1 dev wg_config proto static metric 20050
172.26.0.0/24 dev docker0 proto kernel scope link src 172.26.0.1 linkdown
172.26.1.0/24 dev br-b70272889e99 proto kernel scope link src 172.26.1.1 linkdown
192.168.0.0/24 dev wg_config proto static scope link metric 50
192.168.0.0/24 dev wg_config proto kernel scope link src 192.168.0.201 metric 50
192.168.0.0/24 dev wlp0s20f3 proto kernel scope link src 192.168.0.62 metric 600
192.168.122.0/24 dev virbr0 proto kernel scope link src 192.168.122.1 linkdown
0: from all lookup local
30960: from all lookup main suppress_prefixlength 0
30961: not from all fwmark 0xcaed lookup 51949
32766: from all lookup main
32767: from all lookup default
ip route show table 0 ✔
default dev wg_config table 51949 proto static scope link metric 20050
default via 192.168.0.1 dev wlp0s20f3 proto dhcp src 192.168.0.62 metric 600
default via 192.168.0.1 dev wg_config proto static metric 20050
172.26.0.0/24 dev docker0 proto kernel scope link src 172.26.0.1 linkdown
172.26.1.0/24 dev br-b70272889e99 proto kernel scope link src 172.26.1.1 linkdown
192.168.0.0/24 dev wg_config proto static scope link metric 50
192.168.0.0/24 dev wg_config proto kernel scope link src 192.168.0.201 metric 50
192.168.0.0/24 dev wlp0s20f3 proto kernel scope link src 192.168.0.62 metric 600
192.168.122.0/24 dev virbr0 proto kernel scope link src 192.168.122.1 linkdown
local 127.0.0.0/8 dev lo table local proto kernel scope host src 127.0.0.1
local 127.0.0.1 dev lo table local proto kernel scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local proto kernel scope link src 127.0.0.1
local 172.26.0.1 dev docker0 table local proto kernel scope host src 172.26.0.1
broadcast 172.26.0.255 dev docker0 table local proto kernel scope link src 172.26.0.1 linkdown
local 172.26.1.1 dev br-b70272889e99 table local proto kernel scope host src 172.26.1.1
broadcast 172.26.1.255 dev br-b70272889e99 table local proto kernel scope link src 172.26.1.1 linkdown
local 192.168.0.62 dev wlp0s20f3 table local proto kernel scope host src 192.168.0.62
local 192.168.0.201 dev wg_config table local proto kernel scope host src 192.168.0.201
broadcast 192.168.0.255 dev wlp0s20f3 table local proto kernel scope link src 192.168.0.62
broadcast 192.168.0.255 dev wg_config table local proto kernel scope link src 192.168.0.201
local 192.168.122.1 dev virbr0 table local proto kernel scope host src 192.168.122.1
broadcast 192.168.122.255 dev virbr0 table local proto kernel scope link src 192.168.122.1 linkdown
fe80::/64 dev wlp0s20f3 proto kernel metric 1024 pref medium
local ::1 dev lo table local proto kernel metric 0 pref medium
local fe80::a493:410e:53d0:9d48 dev wlp0s20f3 table local proto kernel metric 0 pref medium
multicast ff00::/8 dev wlp0s20f3 table local proto kernel metric 256 pref medium
Edit #3: I also tried changing the “remote” LAN subnet to 192.168.1.0/24 just in case that overlapping networks are somehow the problem, but this didn’t change the situation, unfortunately.