Can i close the root access ? Without passwd ? Thanks
What do you mean?
Don’t have root acces … ! Have it close, like others distributions like Fedora 33 !
You can disable root login as so:
sudoedit /etc/passwd
change the top line: root:x:0:0::/root:/bin/bash to:
root:x:0:0::/root:/usr/bin/nologin
sudo passwd -d root
you might also want to disable ssh, it’s on by default:
systemctl disable sshd
wouldn’t that delete the password for root, making it password-less? The user could then login as root without typing any password at all. Wouldn’t sudo passwd -l root be the other correct way to lock the account?
both work the same.
deleting the password cuts off root/su/login…
i use -d cause i don’t want any password there at all. -l leaves it there.
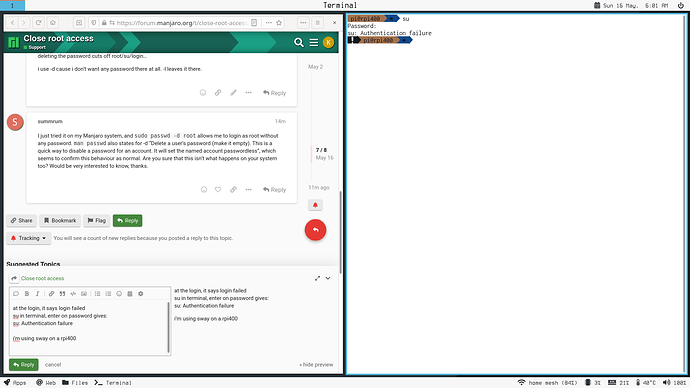
I just tried it on my Manjaro system, and sudo passwd -d root allows me to login as root without any password. man passwd also states for -d “Delete a user’s password (make it empty). This is a quick way to disable a password for an account. It will set the named account passwordless”, which seems to confirm this behaviour as normal. Are you sure that this isn’t what happens on your system too? Would be very interested to know, thanks.
at the login, it says login failed
su in terminal, enter on password gives:
su: Authentication failure
i’m using sway on a rpi400
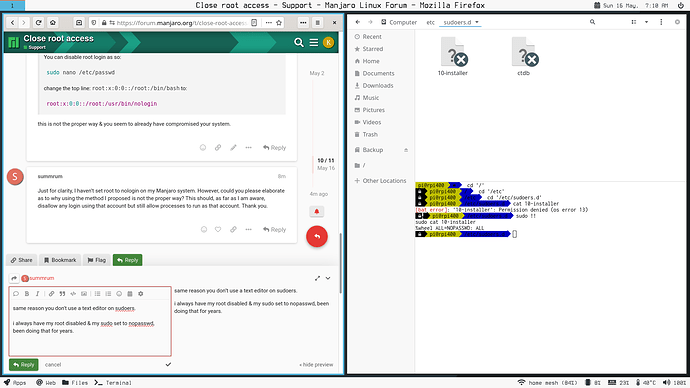
this is not the proper way & you seem to already have compromised your system.
Just for clarity, I haven’t set root to nologin on my Manjaro system. However, could you please elaborate as to why using the method I proposed is not the proper way? This should, as far as I am aware, disallow any login using that account but still allow processes to run as that account. Thank you.
same reason you don’t use a text editor on sudoers.
i always have my root disabled & my sudo set to nopasswd, been doing that for years.
Fair enough, best practice I guess is to use sudoedit so modified my reply to that instead.
Setting the shell to /usr/bin/nologin is perfectly valid but there are other options which do not require editing system files
man usermod
lock the user
sudo usermod --lock root
expire the user
sudo usermod --expire 1970-01-01 root
The default installed /etc/shadow contains the following setting for root. This setting ensures passwordless root is not possible. This setting requires another user with admin rights and this is usually chosen during initial system install. Don’t mess with this unless you know exactly what you are doing.
root:*:14871::::::
interesting, i never used that when i ran debian based os’s to lock root.
i do remember using it for other things.
I have never used systems with the root account locked - but it is possible - you have to ensure another account with sudo access 
I’ve always locked the root account on my home servers, along with strict firewall rules, using a vpn to get access to internal network and ssh key login for one sudo account only (with different password to the sudo account, non-standard ports of course); just about satisfies my paranoia - with regular log checking and backups! Did manage to lock myself out once when I was first starting out though