“Force Block Incoming Connections” is enabled by default in the Global Settings for all apps to block all from LAN and internet.
But this option is in the highest priority and ignores or doesn’t respect your custom whitelists for any apps you want to set.
A tip:
How to switch from “Force Block Incoming Connections” to custom “Incoming Rules” in Global Settings:
-
Disable “Force Block Incoming Connections”
-
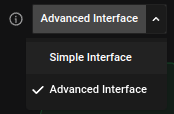
Change “Simple Interface” to “Advanced Interface” for GUI to show a hidden function “Incoming Rules”
-
Add “Allow localhost” and "Block *" in Incoming Rules, the behavior is like “Force Block Incoming Connections”
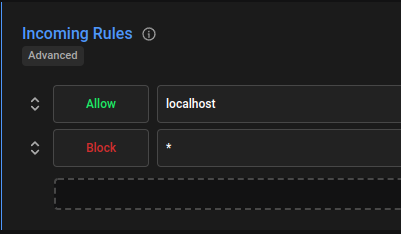
Done, global Incoming Rules respect your custom whitelists for any apps.