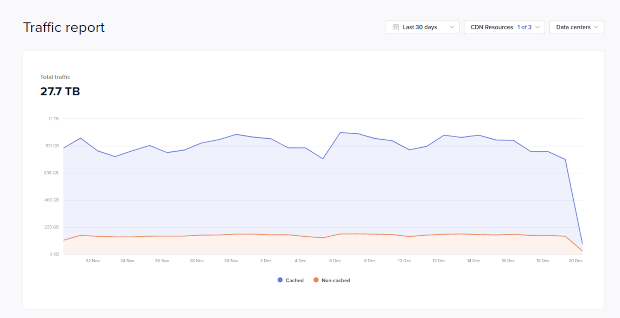
There are too many requests for those AUR databases. Here the last 24h of traffic you guys generate just for that:

Remember that those DBs are just 8 MB in size.
Here a traffic snapshot for the last 30 days just for AUR DB files:
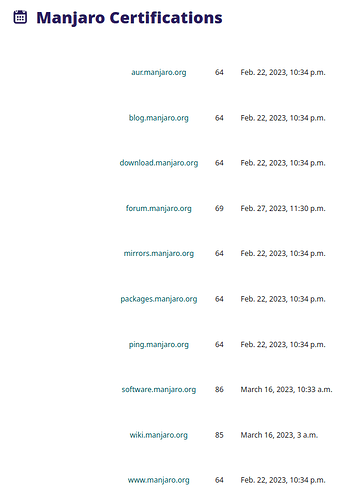
Certificates are all valid:
AUR, Download and Mirrors use the same as our main homepage.
So why do I get those errors?
CDN works like this:
- we have one storage server which gets every 10 Minutes a new DB file from the Arch server
- we purge the files every 15 mins from all CDN nodes
- CDN nodes will fetch the updated DB files from the storage server and cache them again
If you hit a node which is in progress to purge the file you hit an error page. pamac should in that case ignore the error and try to fetch that file again. I assume if you retry to fetch the file you won’t have that error. You only wonder why you have that error and complain.